What a shockingly dull yet all too familiar title! You’ve probably mentally switched off already; clicked on to the latest news or shortened your lunch read because it just seems all like to big an effort.
But be patient. Be courageous. Read on. Those of us fortunate enough to work in cyber security will identify readily with the challenges I set out below. Those of you in senior business positions may gain useful insights. For the rest of my readers? Well, read on as it may prove useful in your life.
My experience has given me many tips, quotes and useful lessons. One particular one is:
“Everyone has an opinion on the RIGHT way to do vulnerability and patch management.”
To illustrate this let’s imagine that it is election time. It doesn’t matter which election - just imagine it’s an election campaign period. The parties are present at the final live TV debate. The host of the show has introduced the campaigners at their podiums.
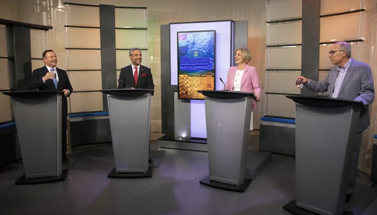
The Chairman of the Board in his finest tailored suit. The ‘business’ representative (Head of Operations) looking pensive shuffling his papers and weighed down with all the worries of the company. The IT Operations Team Lead, not looking refreshed at all after a 48-hour stint addressing an incident. Last but not least we have the Information Security Officer, who looks stressed and run down as she was helping the IT team on the frontlines of the security incident for the last 48 hours. The scene is set, several topics have been covered, the commercial break is over and the director points to the host, who says:
“As we come to the end of our two-hour special broadcast, I have personally learnt a lot. As an outsider, I always believed that keeping systems up to date and secure was as simple as installing an update as soon as its available. Just like on my phone. Who would’ve thought it has so many challenges? So many pitfalls. Perhaps too many complications and viewpoints. To finish, I will now allow each of you a chance to wrap up your views on vulnerability and patch management. Mr. Chairman.”
Confidently, beaming and with a polished tone replied, “Our policies are broad and encompassing, we passionately support the principles and practices of this vulnerability and patch management programme.”
With a puzzled expression the host responded, “Okay, that’s incredibly vague but we’ll press on to Head of Operations”.
“We promote and encourage business processes to support our customer values,” The Head of Operations started. “A conservative, possibly even overly conservative, approach that takes very few chances but believes in a solid steady state as we are. Change must be carefully planned, discussed, considered and then carefully implemented. Validation, of course is also essential.”
“Thank you for that, your view is quite clear,” The host responded, swivelling his chair in the direction of the IT Operations Team Lead. “And so, on to IT.”
The IT Operations Team Lead cleared his throat and paused to gain some clarity of thought through the tiredness. Knowing that what he was about to say may not be what he was thinking or doing but necessary to form a united front, the IT Operations Lead started, “We have a simple, clear policy that supports needs of all we serve. We’ll take on board the issue and analyse it until we are happy or satisfied with all possible outcomes, and then suggest alternatives for all to consider. Once consensus has been reached, we’ll reanalyse, just in case the lapse in time has altered the possible positive outcomes. At this stage we will obviously reinvestigate all possibilities to propose a solution to the new issue that may have no bearing on what the original was. Of course, we do believe in delivering excellent customer service at all times!”. He was glad that was over. He was not keen on this politicking. Head Down, Systems Up – Regardless what is being asked for! Was his motto. He’d been in this game for over twenty years and had outlasted many a CEO, Head of Operations and even ISOs and that, he believed, was down to remaining true to his motto.
With a rather perplexed expression the Host responded, “Thank you for that, and finally our ISO.”
Standing tall, even after the many hours of security incident management, the ISO said, “We are a team with a public agenda of protectionism, we work tirelessly at times often against all odds in encouraging all parties into bipartisan agreement. For the good of the many.” Internally, she was thinking: truth be told our goal is singular at times and while it is protectionism, it is our own skin not the many!
Turning to the camera with its red light on, the Host concluded the broadcast, “And there you have it. You have heard their beliefs. Their manifestos. Their ranging approaches, from extremely cautionary to self-preservation. But whose approach serves the organisation best, whose approach protects the assets, whose approach will ensure trust from the customers. Whose approach will ensure the ongoing existence of the business. Thank you for watching and goodnight”.
While this has been perhaps a light-hearted and imaginative commentary, it is a debate that takes place regularly in organisations throughout the globe. They are even more complex with more agendas and more characters involved. The Chief Finance Officer who is concerned about the impact on the bottom-line. The Sales Director who is concerned about the impact on revenues and the Chief Risk Officer who is always concerned – it’s their job!
So, how do you appease all these views? How do you understand their particular agenda? What is the correct path to follow? What is the approach to ensure the business stays operational, it retains customer trust and that its data stays secure from unauthorised access/use? How does the ISO truly serve all the senior leaders’ initiatives and still achieve the one true goal of vulnerability and patch management?
The Approach
Let’s look at what the one goal is. What is vulnerability and patch management? It contains elements of each of the views and believes around your organisation of the organisation. Patch management is:
“The process for identifying, acquiring, installing, and verifying patches for products and systems to correct security and functionality problems in software and firmware” (NIST SP 800-40)
Quite simple really!
In my experience, vulnerability and patch management can be as complex or as simple as you let it be. The most obvious approach to a successful programme is the simple one. The remainder of this article will give a workable example of one.
Identify: Use tools or a specialist service to scan your critical assets (refer to your asset register where you have classified your assets) for vulnerabilities. The resulting report can then be provided to an appropriate individual(s) to classify the urgency of remediation.
Classify: Within your organisation, an individual - or better yet a small group of individuals who understand the IT environment AND business processes - should be assigned the responsibility of classifying the level of business risks associated with each identified vulnerability. These risks include financial cost (vs. cost of fixing the vulnerability), reputational damage, security risk and privacy violation. This group should also start the remediation phase by making suggestions on how to address them.
Remediate & Validate: This is where a clearly documented approach that governs the decision making can reduce the chances of unnecessary influence from outside forces every time a vulnerability is identified, and a patch is required. The clearer and simpler your process, the higher the chance of success. Patch at times that reduce the impact to the customer, the asset and the business process. Track all changes using your IT department tracking system and record all actions taken – just in case you must undo some work. Once patches have been implemented, re-scan for the vulnerability to ensure the change was effective.
And finally...
While being aware of and displaying empathy towards each party’s agenda and concerns – you should press on. The longer that vulnerabilities remain unfixed, the greater the risk the business carries. So, park the politics and put your assets, your data and your customers to the fore. Do not make campaign style promises or use double speak. Keep your message clear and focused. Deliver, deliver, deliver. Your vulnerability and patch management programme, if done properly, can and will serve your organisation well over the long-term.
Vote for Less Risk!
Vote for Less Disruption!
Vote for Common Sense Vulnerability and Patch Management!





