Fortinet Certificate Revocation Vulnerability
Fortinet Certificate Revocation Vulnerability Advisory
Our Managed Detection and Response Services provide continuous monitoring from a team who’ll neutralise any breaches at speed...
Gain access to malware experts to quickly contain threats and reduce future exposure to attacks...
Integrity360 has been recognised as a Gartner Representative Vendor.
Many organisations are choosing CyberFire MDR to strengthen their defences. Discover how it can protect your business in our brochure.
Cyber attacks often seem faceless, but hidden behind the headlines of financial loss and technical details there are very real human stories.
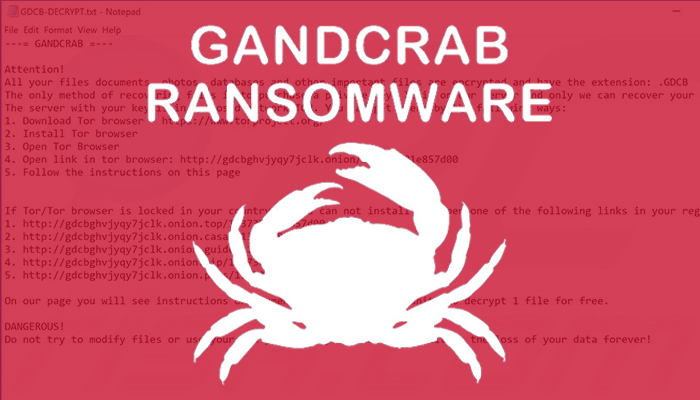
In 2025, we’re witnessing a shift in how ransomware operates, who it targets, and the consequences of falling victim.
Stay ahead of the latest cybersecurity industry developments, advancements and threats, and understand how you can best protect your organisation.
Do you know what your company’s network vulnerabilities are? Businesses that invest in penetration testing do.
If your business handles credit card data, PCI DSS compliance isn’t optional—it’s critical. From retailers and e-commerce platforms to service providers and financial institutions, securing credit card data is critical to customer trust and preventing fraud.
Stay informed with the latest cybersecurity news with our weekly threat roundups.
Confused about cybersecurity? Our A-Z Glossary of terms can help you navigate this complicated industry.
For many small and mid-sized businesses, cybersecurity can feel overwhelming.
SOC 2 certification reflects Integrity360’s continued investment in strengthening cyber resilience for clients across highly regulated and high-risk industries.
Leading Canadian cybersecurity services provider Advantus360 joins Integrity360 creating the group’s first hub in North America
Posts about:
Fortinet Certificate Revocation Vulnerability Advisory
Remote Desktop Services (RDP) Remote Code Execution Vulnerability - Update

Another year and another Data Breach Investigations Report (DBIR) from Verizon.

Remote Desktop Services (RDP) Remote Code Execution Vulnerability

The world’s CIOs, CSOs and CISOs are focused on preventing the next big cyber-attack. The international cyber security community is more interested in the lack of action some companies are taking to reach that goal.

We often take the things we do every day for granted. In the security community, we assume knowledge that’s the norm for us is the norm for everyone else – when it actually isn’t.

The Magecart group was named one of the most dangerous ‘people’ on the internet in 2018. It wasted little time defending its title in 2019.

The cyber security community witnessed brazen attacks, emerging techniques and unfortunately, a general disregard for security best practices over the last year.

Even the world’s most unskilled and inexperienced criminals know it’s always better to sneak in the back door of a shop instead of breaking down the one in the front.
Physical credit card skimmers have been a fan favourite of criminals over the past decade. Now, hackers have developed their own digital version of the tool and are deploying it within the online checkout process.
If you laid the source code of all the malware strains in the world together, it would probably wrap around the world a few times over.
There’s been some big headlines in the news about data breaches over the last few years. An attack on Equifax exposed the sensitive information of 143 million U.S. citizens; Yahoo! saw hackers compromise 3 billion accounts.