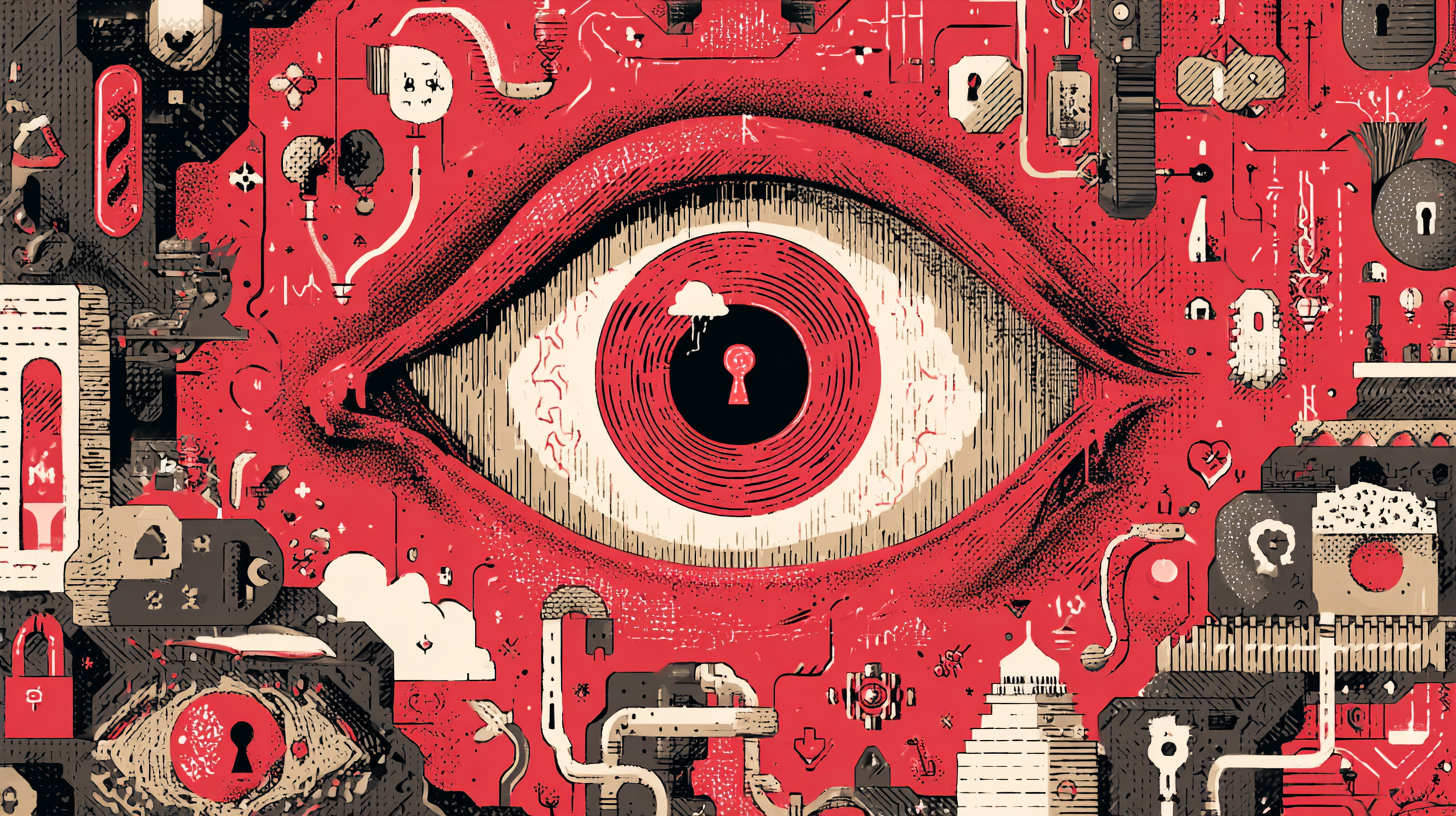
Cyber bounty hunters: how bug bounty programmes keep your business secure
In the world of cyber security, attackers are always innovating and testing the boundaries of systems, networks, and applications to find the gaps that no one else has spotted. For organisations, the challenge is keeping ahead of them. Traditional penetration testing is a powerful and necessary tool, but it’s not the only one available. Enter the modern-day bounty hunters: highly skilled ethical hackers scouring your systems for exposures before malicious actors can exploit them. This is the world of bug bounties.