The Twitter Hack: Why Organisations Must Now Address Physical Social Engineering Risks
When we think of cyber-attacks, we often think of a skilled operation that targets an organisation’s network but attacks have become much more multi-layered.
Our Managed Detection and Response Services provide continuous monitoring from a team who’ll neutralise any breaches at speed...
Gain access to malware experts to quickly contain threats and reduce future exposure to attacks...
Integrity360 has been recognised as a Gartner Representative Vendor.
Many organisations are choosing CyberFire MDR to strengthen their defences. Discover how it can protect your business in our brochure.
Cyber attacks often seem faceless, but hidden behind the headlines of financial loss and technical details there are very real human stories.
In 2025, we’re witnessing a shift in how ransomware operates, who it targets, and the consequences of falling victim.
Stay ahead of the latest cybersecurity industry developments, advancements and threats, and understand how you can best protect your organisation.
Do you know what your company’s network vulnerabilities are? Businesses that invest in penetration testing do.
If your business handles credit card data, PCI DSS compliance isn’t optional—it’s critical. From retailers and e-commerce platforms to service providers and financial institutions, securing credit card data is critical to customer trust and preventing fraud.
Stay informed with the latest cybersecurity news with our weekly threat roundups.
Confused about cybersecurity? Our A-Z Glossary of terms can help you navigate this complicated industry.
For many small and mid-sized businesses, cybersecurity can feel overwhelming.
SOC 2 certification reflects Integrity360’s continued investment in strengthening cyber resilience for clients across highly regulated and high-risk industries.
Leading Canadian cybersecurity services provider Advantus360 joins Integrity360 creating the group’s first hub in North America

When we think of cyber-attacks, we often think of a skilled operation that targets an organisation’s network but attacks have become much more multi-layered.
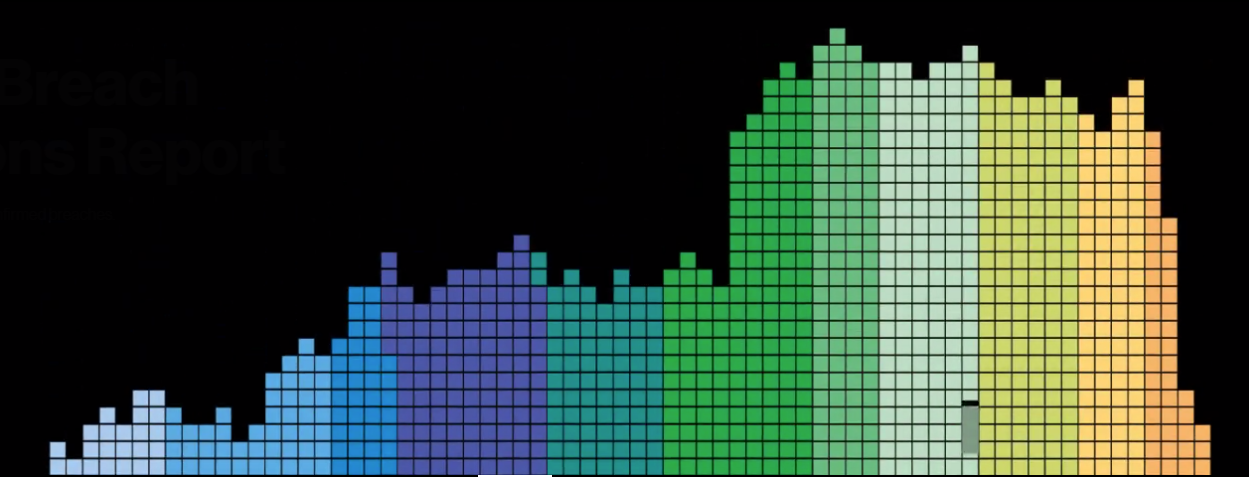
It would take hours to read through the 100+ pages of the Verizon’s Data Breach Investigations Report (DIBR) which takes the pulse of the security landscape for companies and organisations every year.

Microsoft Vulnerability in Windows DNS

CVE-2020-5902

Privileged Account Management (PAM) has been placed at #1 for last two consecutive years (2018 & 2019) in Gartner’s Top 10 Security Projects. This is due to the fact that nowadays, with an ever-expanding infrastructure like on-premises, cloud, IoT, DevOps, mobile devices and SaaS Business Applications, classical Perimeter Security is not as effective as it used to be due to so many control points and gateways. Furthermore, privileged accounts exist on every asset and system out there, not forgetting about Non-Human Privileged Accounts that are even more difficult to monitor and track (e.g. vulnerability scanners, RPA, or Secrets in Jenkins, etc.)

Very few of us have experienced times like this in our lifetime. A global invisible threat to our lifestyle, our economics, our health and our very existence in some cases, has filled our daily lives.

Integrity360 is aware of an increased in DDoS attacks globally which we would like to remind our clients to remain vigilant about.

Integrity360 has just been awarded a Secure SD-WAN specialisation by Fortinet. This now complements the company’s Data Centre Specialisation and offers assurance to Integrity360 clients that the highest levels of qualifications are in place to advise and deliver SD-WAN solutions effectively and in line with best practices. Integrity360 is the first and only partner in Ireland to be awarded this specialisation and one of only two partners in the UK with it.

Many companies find themselves closing their doors these days for an uncertain period of time. Social distancing and self-isolation are the right moves in the midst of what the world is dealing with, but just because businesses are taking these steps doesn’t mean that cybercriminals will respect them.

While it’s estimated that over 50% of employees globally work outside of their main office for at least 2.5 days per week, the advancement of Covid-19 in recent weeks is challenging all organisations to mobilise their entire workforces, not just a select few departments. This mass mobilisation is creating huge challenges for cyber security teams.
Last month, Check Point noted that their latest Global Threat Index for January 2020 showed cyber-criminals exploiting interest in the global Coronavirus pandemic. The aim of these cyber-criminals was to spread malicious activity, with several spam campaigns relating to the outbreak of the virus.

While the effects of the Coronavirus develop, businesses across the world are turning to remote working to ensure the safety of their employees as well as the continuity of their services.